There are many high-potential use cases for blockchain technology including real-world asset tokenization, cross-border payments, decentralized finance applications, store of value, and more. Another intriguing use case that is gathering more attention is decentralized identity.
More people are becoming increasingly wary of handing over private personal data to centralized businesses due to security concerns. For example, upon downloading or signing up for a web service, users most likely have to register some combination of the following: personal name, email address, home address, phone number, etc. However, these centralized businesses and applications have not been able to consistently securely store this information as hackers have regularly hacked databases to access personal data.
Now by leveraging decentralized blockchain technology, personal identity has the potential to become verified and stored in a more secure and decentralized manner. This use case for decentralized identity comes from decentralized identifiers (DIDs) which can transform the concept of one’s online identity.
One particular project focusing on decentralized identity is Cardano Connect (CNS), a social media and decentralized identity platform that uses DIDs for people to choose a simple .ada extension to represent their personal, verified identities in the Cardano blockchain ecosystem. This enables its users to choose and verify their online identity name (using a .ada extension), and also use it as a wallet address to conduct transactions when using decentralized applications built on Cardano.
It’s a relatively understated technology that has not drawn as much attention as others due to its nascency.
In this blog, there is a further discussion about DIDs and their transformative potential for users to securely manage their identity.
Related reading:
At a basic level, a decentralized identifier (DID) is a new class of global identifier for the internet. These DIDs are an emerging piece of a new type of decentralized digital identity and public key infrastructure (PKI) for web services both in the realm of Web2 (centralized web) and also for Web3 (blockchain-based decentralized web). There is much potential for this technology in nearly all levels of human communication.
The use of unique identifiers has increased since the start of global communication as users and entities have to rely on them daily. These identifiers could be communication addresses for things such as (but not limited to):
- Telephone numbers
- Email addresses
- Usernames on social media
and ID numbers for personal items such as:
- Passports
- Driver’s licenses
- Bank accounts
- National IDs
and also product identifiers for things such as:
- Serial numbers
- Barcodes for inventory
- Warehouse codes
In most cases, control of these identifiers is outside the user’s purview. They are created and controlled by centralized entities and authorities that have the power to nullify them at any point. Plus, their validity is limited either by a country’s jurisdiction or by the format of a particular communications protocol. If the organization keeping track of them fails (a government, a company, an NGO, a university, etc.), the identifiers can be banished forever. They are also vulnerable to online security breaches by malicious third parties which can result in personal identity theft.
In this context of the global use of identifiers, DIDs are defined as a new type of globally unique identifier.
Read more:
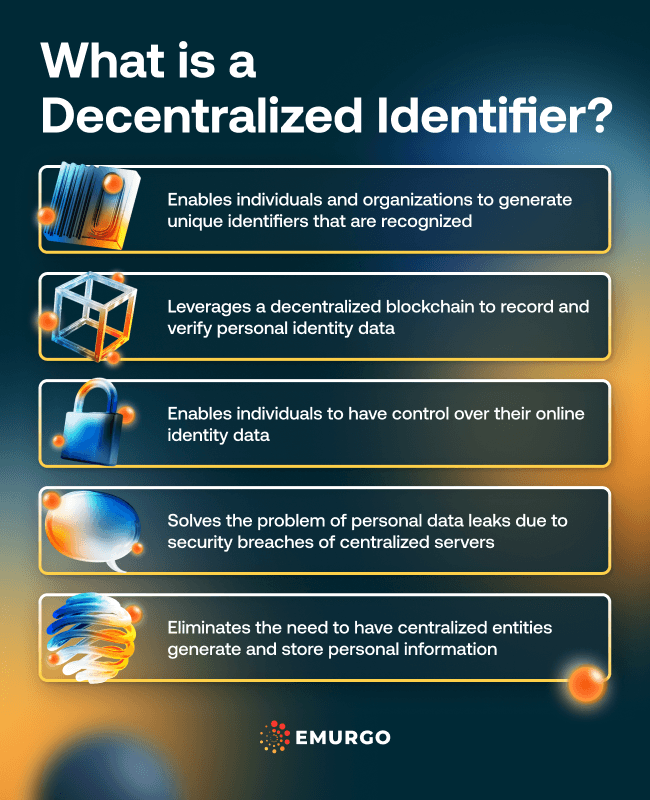
DIDs are designed to enable individuals and organizations to generate unique identifiers that are recognized globally using a verifiable system. Cryptographic proofs like digital signatures leveraging a decentralized blockchain can secure these new classes of identifiers.
Since DIDs tap a common shared system or decentralized blockchain to generate them, entities and users can create as many as they need. Each DID is under the control of the user by way of cryptographic primitives which allow for access customization. Each DID also contains the personal information judged to be necessary for a task.
For example, to enter a bar a person needs to be of legal drinking age. A DID can be configured to validate that this person is older than 21 without revealing the age of the individual, the date of birth, or any other unnecessary personal information. This information would also be out of the hands of any centralized entities. It would only provide binary proof (yes/no) that the person is older than 21.
DIDs refer to a new standard for globally valid identifiers that don’t require a central authority to generate or track them. They are generated by the users themselves and these are in turn recorded or stored in a distributed ledger or decentralized blockchain network such as Cardano. This ledger acts as the repository that other organizations can then access to verify the DIDs and the information contained in them.
The method required to generate a DID goes through a series of systems that interact with each other to create the identifier. There is a general scheme that was created by the W3C organization, a global open-source project dedicated to DID technology.
The three major components of the system are:
DID Subject: The entity looking to prove something with the DID such as a product, a location, a company, a device, or a real person.
DID Document: The information recorded by the DID regarding its subject plus the mechanisms behind the identifier. It could be the cryptographic primitives behind the way the entity controls the DID.
Verifiable data registry: Records the DIDs and is used to verify the information contained in them. This can be a blockchain network and its distributed ledger.
All these modules are used to create an identifier that proves a certain piece of information is correct, that it belongs to a proper user, and can be verified by any participant. DIDs eliminate the need to have central authorities generate information and also store important personal information. Both are now given control to the general public and secured by a distributed network of nodes or servers incentivized to maintain a decentralized blockchain network.

Are you looking to stay up-to-date on decentralized identity features within Cardano and other Cardano ecosystem-related news?
Then, follow EMURGO on X to receive regular updates and announcements including weekly updates and a monthly newsletter.
About EMURGO
- Official Homepage: emurgo.io
- X (Global): @EMURGO_io
- YouTube: EMURGO channel
- Facebook: @EMURGO.io
- Instagram: @EMURGO_io
- LinkedIn: @EMURGO_io
Disclaimer
You should not construe any such information or other material as legal, tax, investment, financial, or other advice. Nothing contained herein shall constitute a solicitation, recommendation, endorsement, or offer by EMURGO to invest.



